24/7 Managed SOC for your organization
Not your own security team? No problem. Our SOC monitors your entire IT environment with SIEM monitoring, threat hunting and incident response, staffed 24/7 by certified analysts.
What can go wrong without 24/7 SOC monitoring
Without active log monitoring, SIEM correlation, and threat hunting, you're vulnerable when it matters. These are the risks that a SOC prevents.
Ransomware attacks
Ransomware encrypts your entire infrastructure in minutes. Without active SIEM correlation and 24/7 triage, the first signals are missed and the damage amounts to millions.
IBM Cost of a Data Breach 2025
Invisible attackers in your network
Without threat hunting and behavioral analysis, attackers remain undetected in your environment for months. The longer the dwell time, the greater the damage to systems and data.
IBM Cost of a Data Breach 2025
AVG fines & reputational damage
Without structured incident handling and audit-ready logging, you are not compliant. The Data Protection Authority can impose fines that are substantial, in addition to losing customer trust.








































Why our managed SOC service?
Detection that is constantly getting smarter
After each incident, we refine our detection rules based on the MITRE ATT&CK framework. New attack techniques are immediately translated into better detection for your environment.
Actively looking for what others miss
Our analysts don't wait for alerts. They proactively hunt for hidden threats in your environment based on threat intelligence and behavioral analysis.
Clear agreements about who does what
Each alert is classified by severity (P1 to P4) with fixed response times and escalation paths. You know exactly what happens in the event of an incident beforehand.
Works with your current IT environment
From cloud to on-premise: our SOC connects to your existing firewalls, endpoints and identity systems. No vendor lock-in, no blind spots.
How our SOC service works
Our approach is pragmatic, transparent and fully tailored to your organization. Here's how our SOC works operationally:
Log Collection & Detection
Logs from endpoints, firewalls, cloud environments and identity systems are collected and correlated in real time via our SIEM platform. Automated detection rules identify anomalies immediately, even outside office hours.
Triage & Classification
Each alert is validated by our analysts and classified by severity (P1 to P4). False positives are filtered, real threats are mapped to MITRE ATT&CK contextual analysis tactics.
Incident Response & Escalation
In the event of a confirmed incident, we intervene via the agreed escalation model. P1 incidents are arrested within 15 minutes. Our response includes isolation, forensics and direct communication to your team.
Detection Engineering & Improvement
After each incident, we analyse the root cause and attack path. New detection rules are being written, existing rules are being refined. Your security posture is continuously being tightened. This way, every attack makes you more resilient.
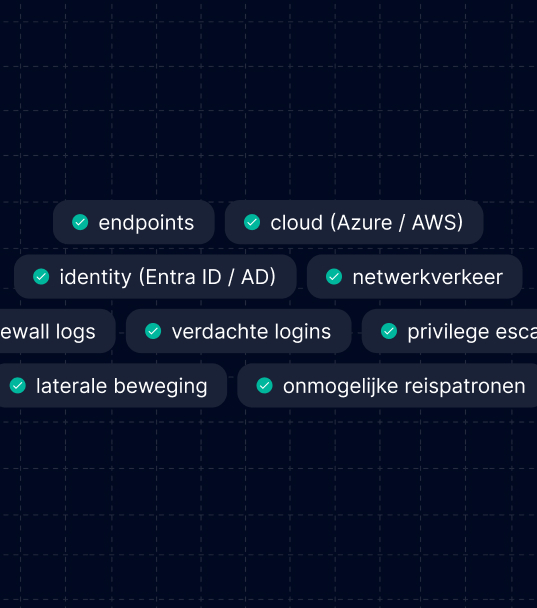
Full SOC monitoring across your entire IT landscape
Our SOC correlates logs and events from your entire IT landscape. From endpoints to the cloud, from identity to network traffic. We monitor every attack surface and detect threats across the board.
Why choose Aumatics' 24/7 managed SOC?
Without 24/7 monitoring, threats go unnoticed. Our SOC detects and responds immediately to suspicious activity.
Without Aumatics SOC
Possible issues you run into:
Late detection
Incidents are only discovered when the damage is already visible. Without a SIEM correlation, you miss the early signals.
Minimal coverage
Attacks occur just outside office hours. Without a 24/7 staffed SOC, no one intervenes.
No correlated threat picture
IT teams lack the tooling and time for log correlation and threat hunting across the entire landscape.
No demonstrable compliance
Vulnerable to ISO 27001 and NIS2 audits due to a lack of structured monitoring and incident handling.
With Aumatics SOC
24/7 threat visibility. Respond faster. Less risk.
SIEM-based real-time insight
Correlated log data from your entire environment, from endpoints and cloud to identity and network.
P1 response time <15 minutes
Certified analysts initiate immediate incident response to critical threats.
staffed 24/7 by SOC analysts
Even at night, on weekends and holidays. Not tooling-only, but people who intervene.
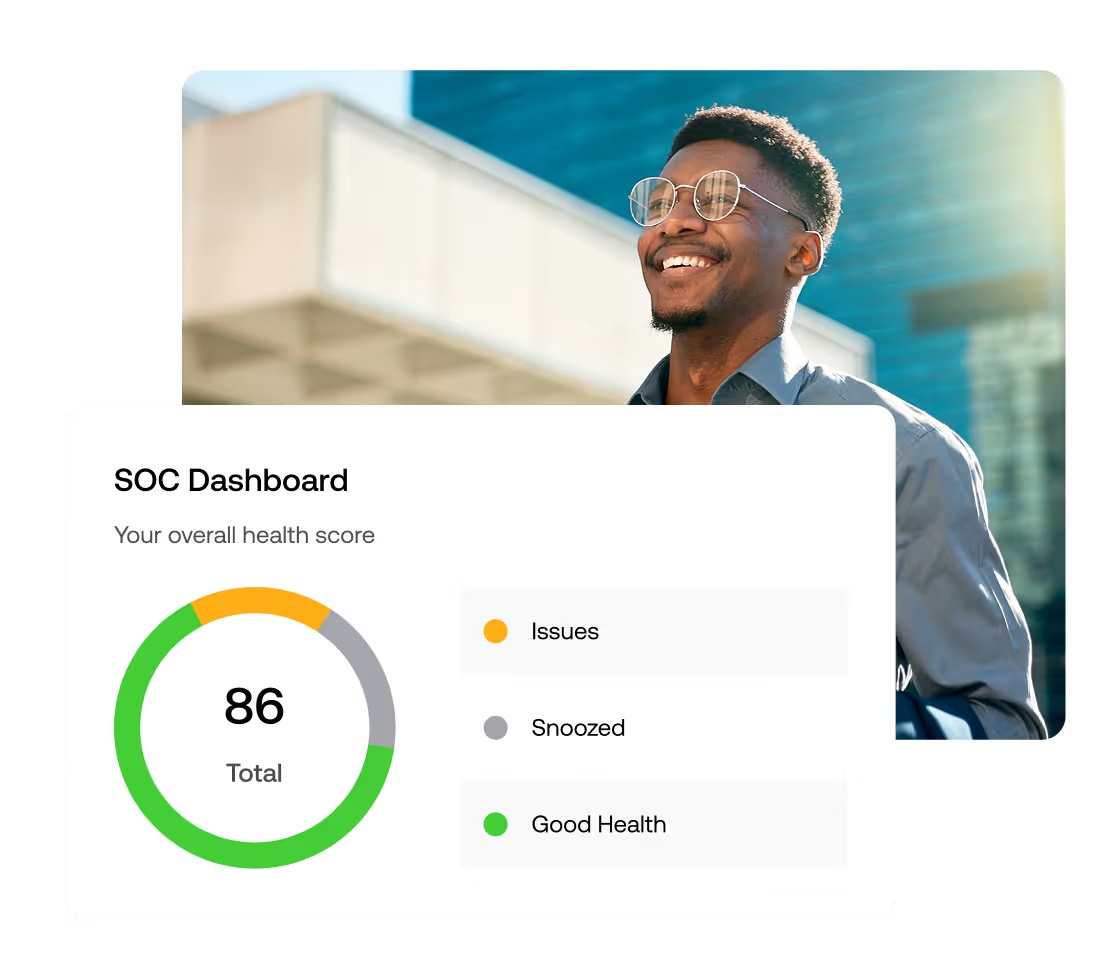
Fully managed, no need for your own SOC
No extra staff and no SIEM management. You receive periodic reports and have access to a dashboard with real-time insight into your security posture.
Audit-ready and compliant
Complies with ISO 27001, NIS2 and GDPR. Complete logging and reporting that allows you to immediately demonstrate that you are complying with your duty of care.
We work with the best partners for your security
We manage environments built on Palo Alto, Fortinet, WatchGuard, and other enterprise solutions. Not as standalone components, but as a coherent infrastructure. You don't have to compromise on existing investments. We ensure alignment, standardisation, and clear management processes.
Security according to demonstrably high standards
When it comes to security, you don't want to rely on separate agreements or good intentions. With our ISO 27001 certification, you know that information security is structurally organized, controlled and improved.

Broad coverage with central expertise
You get one central point of contact, with the strength of a regional presence and specialized hubs across the country. This way, you benefit from local involvement and shared knowledge.

Trusted by IT leaders in the Netherlands
The IT and security partner of Dutch organizations for more than 25 years.
FAQ
What you should know before getting started with our SOC
These are the questions that organizations often ask us. Do you have another question?
Is your question not listed?
No problem. Feel free to let us know what questions you have!
If your organisation depends on IT systems, you want to know what's happening in your environment. Without a SOC, threats are often only discovered once damage has already been done. A SOC provides continuous monitoring and rapid detection of incidents. If you have no IT systems or they have no direct impact on your organisation, then you don't need a SOC. Otherwise, we strongly recommend engaging one.
Many organisations have multiple security tools but lack central oversight. A SOC connects these signals and analyses them continuously. This prevents important alerts from going unnoticed.
Costs depend on your IT environment, number of systems, and monitoring needs. That's why we typically start with a short analysis of your environment. Based on that, we put together a proposal that fits your risk profile and scale.
Our SOC detects suspicious activities and analyses them immediately. In the event of an incident, we get in touch and advise on the right actions. Depending on the agreed Service Level Agreements (SLAs) and escalation models, we can also take action ourselves in your environment and isolate or shut down the threat, if agreed in advance.
Yes. Our SOC takes monitoring, analysis, and alert triage off your hands. Your IT team only receives alerts that are genuinely relevant.
That way, you can focus on management and projects instead of security alerts.
When a threat is confirmed, our analysts immediately start incident response following a pre-agreed escalation model.
Wondering how we can further help your organization?
Tell us about your organization and security issues. Our specialists are happy to help you find the approach that best suits your situation, without obligations.
Thanks!
We received your message and will get back to you as soon as possible. We'll send you a confirmation message.




