Managed EDR die endpoint-aanvallen detecteert en stopt
Onze analisten monitoren je laptops, servers en werkstations 24/7. Verdacht gedrag wordt direct gestopt, voordat schade ontstaat.
Antivirus alone doesn't see what's really happening on your endpoints
Modern attackers use legitimate tools that don't trigger a signature. Without behavioral detection, they remain invisible.
Fileless attacks remain invisible
Attackers are exploiting PowerShell and WMI. Not a malicious file, so signature-based antivirus doesn't sound the alarm.
Attacks are detected too late
Without continuous telemetry, a compromise remains invisible for months. Attackers then already have plenty of time to cause damage.
No forensic context in case of incidents
In the event of an incident, you don't know how it started or which systems were affected. As a result, research and repair take much more time.








































Detection, analysis and response at one layer deeper than antivirus
EDR is more than just technology. It requires adequate management, continuous monitoring, analysis and rapid follow-up.
Behavioral detection instead of signatures
We analyse the behaviour of processes, scripts and users. Suspicious patterns are recognized, even without a known malware signature.
Continuous telemetry from each endpoint
Process starts, network connections and file modifications are continuously recorded. An attack can thus be traced back to the first suspicious process.
Process tree analysis with each alert
Our analysts see the entire chain: which process started which process, with which command line. No separate alerts, but context.
Active response, not just detection
In the event of a confirmed threat: device isolation, process kill and IOC sweep across your entire endpoint park. Act immediately, don't wait.
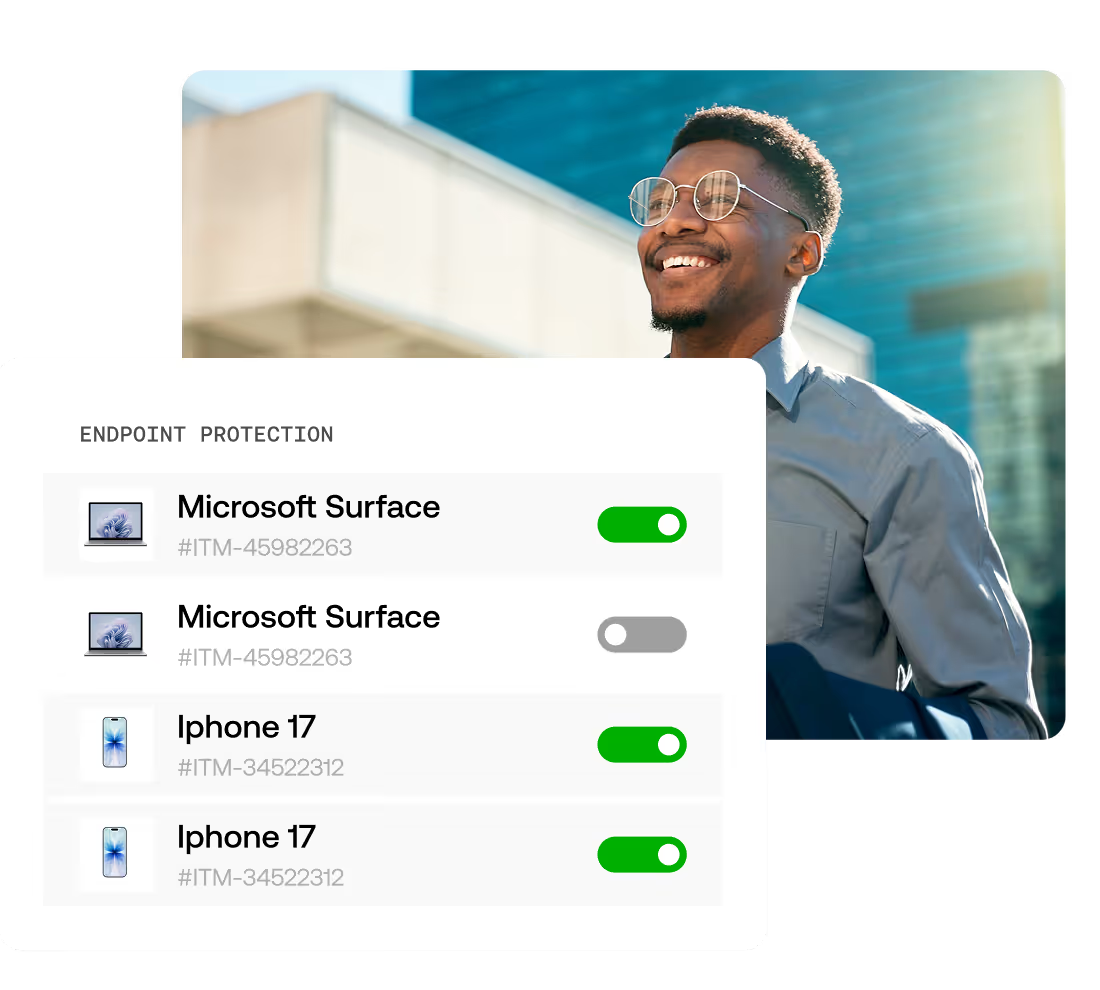
How we implement EDR on your endpoints
Controlled deployment into your existing environment, without disrupting users.
Endpoint inventory
We map out which laptops, servers and existing tooling are active. This is how we work seamlessly alongside Microsoft Defender AV.
Deployment of the EDR Agent
The agent is being rolled out in phases on laptops, servers, and workstations. Runs lightly and with no noticeable impact on performance.
Tuning detection rules and telemetry
Detection rules are tailored to your environment. In this way, we prevent false positives and increase signal quality.
24/7 monitoring and active response
The analysts in our Security Operations Center monitor continuously. In the event of threats, device isolation, process kill and an IOC sweep follow.
Why choose Aumatics managed EDR alongside Microsoft Defender
Microsoft Defender Antivirus is a good starting point and you don't have to turn it off. However, for organizations with business-critical systems, we recommend using a more mature EDR solution in addition, for the following reasons:
Microsoft Defender only, no managed EDR
There is a greater risk that attacks will only be detected when systems are as contaminated.
Attacks are discovered (too) late
Without telemetry, you miss the moment when a process shows suspicious behavior.
No forensic context
You don't know how an attack started or which systems were affected.
No concrete response
Your IT team must act ad hoc. That takes time and increases the damage.
With managed EDR by Aumatics
Better control over advanced threats and act more proactively.
24/7 Behavioral Detection
Suspicious patterns detected immediately, including fileless attacks and suspicious PowerShell.
Process tree with each alert
The entire chain is visible: which process, which command line, which connections.
Device isolation within minutes
In the event of a threat, the endpoint is immediately disconnected. Dissemination stopped.
Process kill and IOC sweep
Malicious processes ended, same indicators searched for on all your endpoints.
Report after each incident
What happened, what actions were taken, and what has been tightened up.
Built on proven technology.
We manage environments built on Palo Alto, Fortinet, WatchGuard, and other enterprise solutions. Not as standalone components, but as a coherent infrastructure. You don't have to compromise on existing investments. We ensure alignment, standardisation, and clear management processes.
Security according to demonstrably high standards
When it comes to security, you don't want to rely on separate agreements or good intentions. With our ISO 27001 certification, you know that information security is structurally organized, controlled and improved.

Broad coverage with central expertise
You get one central point of contact, with the strength of a regional presence and specialized hubs across the country. This way, you benefit from local involvement and shared knowledge.

Trusted by IT leaders in the Netherlands
The IT and security partner of Dutch organizations for more than 25 years.
FAQ
What you should know before getting started with our managed EDR
These are the questions that organizations often ask us. Do you have another question?
Is your question not listed?
No problem. Feel free to let us know what questions you have!
Traditional antivirus mainly focuses on known malware. EDR looks at behaviour on endpoints and can therefore also detect new or advanced attacks. That's why many organisations combine their existing endpoint protection with EDR.
Modern EDR solutions are designed to run lightly on systems. In most environments, users notice no difference in performance. During implementation, we make sure the configuration is properly matched to your environment.
EDR generates alerts that require analysis. That's why many organisations choose to combine EDR with our Security Operations Center (SOC) or Managed Detection and Response (MDR) services. This way, your IT team only receives alerts that are genuinely relevant, while we handle most alerts on your behalf.
EDR continuously monitors endpoints and analyses suspicious activities in real time. Many threats are therefore spotted at an early stage. This helps stop attacks before they can spread further.
EDR is usually installed on laptops, workstations, and servers. This can cover Windows, macOS, and Linux systems, depending on the solution. That way, you gain visibility across virtually all endpoints within your organisation.
Suspicious activities are flagged and analysed immediately. Depending on the situation, a system can be isolated or a process stopped, for example. This limits further damage.
Schedule an EDR intake call with a security expert
Tell us about your organization and security issues. Our specialists are happy to help you find the approach that best suits your situation, without obligations.
Thanks!
We received your message and will get back to you as soon as possible. We'll send you a confirmation message.




